Countering the financing of terrorism is a major focus for regulators overseeing financial services and fintech companies. With the growth of new payment methods, digital assets, and cross-border products, terrorist groups continue to find new ways to move money.
That puts growing pressure on fintechs to understand how their products could be misused, even when transactions appear small or routine.
This article explains what countering the financing of terrorism, or CFT, means for today’s fintech landscape. You’ll also learn how terrorist financing works in the financial system, how it differs from money laundering, and why activities like charity payments or online fundraising can raise concerns.
What Does CFT Stand for in Financial Services?
CFT (Countering the Financing of Terrorism) refers to the laws, controls, and processes designed to stop money from reaching terrorist groups. The focus isn’t just on catching criminals after the fact. It’s about identifying how funds are raised, moved, and used before they support criminal activity.
In simple terms, CFT looks at the money side of terrorism. Terrorist organizations need funding to operate. That money can come from many sources, including:
Donations
Business revenue
Charities
Online campaigns
It can also move through banks, fintech apps, payment platforms, or crypto wallets. CFT controls are meant to spot those flows and interrupt them.
For example, a series of small transfers sent to accounts in high-risk regions might not look suspicious on their own. Over time, though, patterns can emerge that suggest coordinated activity. CFT programs are built to detect those patterns, escalate concerns, and report them to the right authorities when needed.
What Is the Countering Financing of Terrorism Act?
There isn’t a single law in the United States called the “Countering Financing of Terrorism Act.” Instead, CFT requirements come from a group of laws and regulations that work together to limit how terrorist groups access the financial system.
In the US, much of the CFT framework comes from the USA PATRIOT Act and the Bank Secrecy Act. These laws expanded the responsibilities of financial institutions after 9/11. They require firms to:
Know who their customers are
Monitor transactions
Report suspicious activity that could relate to terrorism or other serious crimes
For example, if a fintech notices repeated transfers to individuals or entities linked to high-risk regions, the firm may be required to review that activity and file a report. The obligation doesn’t depend on whether the funds are illegal. What matters is the potential connection to terrorist activity.
How Terrorist Financing Works in the Financial System
Terrorist financing often blends into normal financial activity. Funds may come from lawful sources and move through common financial products, which isn’t always obvious at first glance.
Below is a high-level overview of how terrorist financing typically moves through the financial system and where risks tend to arise.
Differences Between Terrorist Financing and Money Laundering
Terrorist financing and money laundering are closely linked, but they aren’t the same thing. Mixing them up can lead to gaps in how risks are identified and managed.
Money laundering usually starts with illegal funds. The goal is to hide where the money came from and make it look legitimate.
Terrorist financing often works the other way around. Funds may be earned legally, through salaries, donations, or business activity, but are later used to support terrorism. Because of this, CFT controls focus heavily on patterns, destinations, and connections.
It’s less about where the money came from and more about how it moves and who ultimately benefits.
Aspect | Terrorist Financing | Money Laundering |
|---|---|---|
Source of funds | Often legal, such as salaries, donations, or business income | Typically illegal, such as fraud, trafficking, or corruption |
Primary goal | Support terrorist or extremist activity | Hide the illegal origin of funds |
Transaction size | Often small and repeated | Can involve large sums or complex transfers |
Typical patterns | Coordinated transfers, specific destinations, linked recipients | Layering, structuring, and use of shell accounts |
Key compliance focus | How money moves and who ultimately benefits | Where the money came from and how it’s disguised |
Common red flags | Donations, payments to high-risk regions, and links to watchlisted entities | Unusual cash activity, rapid movement between accounts |
How Legitimate Funds Are Used to Finance Terrorism
In many cases, the funds for terrorist financing start out clean and come from everyday sources. That’s why risk is often hard to spot.
Common sources include salaries, business revenue, personal savings, and donations. Charities and nonprofits can also be misused, sometimes without their knowledge. In other cases, funds move through legitimate businesses that mix lawful activity with hidden support for terrorist groups.
Corruption can also play a role. In some regions, bribes or diverted public funds end up supporting extremist activity. For instance, a local official might abuse their position to redirect money, or a business owner might be pressured to contribute. On paper, the transactions look like normal expenses or transfers.
For fintechs, the key takeaway is that legality at the source doesn’t remove risk. When legitimate funds move through certain geographies, networks, or patterns, they can still raise serious CFT concerns that need closer review.
Why Terrorist Financing Often Involves Small Transactions
Terrorist financing is often built around small transactions because they attract less attention and are easier to blend into everyday financial activity.
These transactions also make cross-border movement easier. This is because small transfers are less likely to trigger automated thresholds, reviews, or delays, allowing funds to move more quietly through banks, fintech platforms, or crypto networks.
For compliance teams, this means size alone isn’t a reliable signal. Patterns, timing, recipients, and connections between accounts often matter more than dollar amounts when identifying terrorist financing risk.
Why Does Countering the Financing of Terrorism Matter for Fintechs?
CFT carries real consequences for fintech companies. The way these risks are handled can affect regulatory standing, partnerships, and the ability to launch or scale products. Here are the key reasons regulators pay close attention to how fintechs manage CFT risk.
Fintech products make it easier to move funds quickly: Many fintech platforms are built for speed and convenience. Instant payments, digital wallets, and global transfers can be misused if controls don’t keep pace. For example, rapid peer-to-peer transfers or cross-border payments can allow funds to move before unusual patterns are noticed.
CFT risk creates direct regulatory exposure: Regulators expect fintechs to identify and manage terrorist financing risk as part of their broader financial crime programs. Gaps in CFT controls can lead to exam findings, enforcement actions, or limits on business activities, even when no intentional wrongdoing is found.
CFT failures can disrupt partnerships and licensing: Banks, payment networks, and other partners often review a fintech’s CFT controls as part of due diligence. Weak programs can delay approvals, restrict access to key partners, or create issues during licensing and renewal processes.
Regulatory expectations grow as fintechs expand: As products become more complex or enter new markets, regulators expect CFT controls to scale with them. A program that worked for a single product or region may not hold up once a fintech adds crypto, cross-border services, or new customer types.
Terrorist financing risk isn’t always obvious: Unlike other financial crimes, terrorist financing often involves lawful funds and ordinary transactions. That means fintechs can be exposed even when customers appear low risk and activity looks routine.
CFT gaps can surface during exams and audits: Regulators don’t just look for policies on paper. They review alerts, escalation decisions, and documentation. Weak recordkeeping or inconsistent reviews can raise concerns, even if the firm hasn’t identified known terrorist links.
Reputational impact can follow compliance failures: Public enforcement actions related to terrorist financing attract attention. For fintechs that rely on trust from users, investors, and partners, that exposure can have lasting effects beyond regulatory penalties.
Product design choices can increase or reduce risk: Features like anonymous accounts, rapid onboarding, or limited transaction visibility can increase CFT exposure if not balanced with controls. Regulators expect fintechs to understand how product decisions affect risk.
How Countering the Financing of Terrorism Works in Practice
CFT in financial services relies on a set of controls that work together. Each one looks at risk from a different angle, helping firms identify, review, and respond to suspicious activity as it moves through their systems.
Customer Due Diligence and Identity Verification
Customer due diligence (CDD) is one of the first lines of defense against terrorist financing. It focuses on knowing who your customers are and understanding how they plan to use your product.
At a basic level, this means collecting and verifying identity information during onboarding. For an individual, that might include a government ID and proof of address. For a business, it often involves ownership details, control persons, and the nature of the company’s activities.
CDD doesn’t stop at onboarding. Fintechs are expected to build a clear picture of expected behavior. For example, a customer signing up for a domestic payments app should raise questions if they quickly start sending repeated transfers to high-risk regions. When activity doesn’t line up with what was expected, it’s a signal to look closer.
Regly supports this process by streamlining data collection, validation, and risk screening, making it easier for teams to embed CDD directly into onboarding workflows.
Sanctions and Terrorist Watchlist Screening
Sanctions and watchlist screening play a direct role in how fintechs manage terrorist financing risk. It gives teams a way to identify known threats before they move through the platform.
Most fintechs screen customers during onboarding and continue screening as transactions occur. Teams check names, businesses, and counterparties against government and international lists that change frequently. Because those lists evolve, screening has to stay ongoing rather than static.
When a name or transaction triggers a match, the work doesn’t stop there. A reviewer looks at the details, compares identifying information, and decides whether the alert can be cleared or needs escalation. Many matches turn out to be false positives, but each decision still needs a clear record.
This is where risk scoring plays an important role. Using Regly’s risk scoring tool, compliance teams can assess customer, transaction, and geographic risk together to better understand which alerts deserve closer attention. This risk-based approach helps reduce false positives, prioritize meaningful risk signals, and support a more effective CFT program.
The review process is what regulators focus on most. They want to see consistent decision-making, documented reasoning, and evidence that screening results lead to action when risk appears.
Transaction Monitoring for Terrorist Financing
When monitoring or screening raises concerns, fintech teams need a clear way to respond. That is where suspicious activity reporting comes in, providing a bridge between internal review and regulatory notification.
To manage this process effectively, teams need transaction monitoring systems that do more than generate alerts. This is where Regly’s AML transaction monitoring tool comes into play.
It helps detect suspicious patterns earlier using premade and customizable rules built from real-world compliance experience. Flagged transactions move through automated escalation workflows, helping teams apply consistent judgment, reduce false positives, and document decisions clearly.
Suspicious Activity Reporting and Escalation
When transaction monitoring or screening raises concerns, fintech teams need a clear way to respond. Suspicious Activity Reporting (SAR) is how those concerns move from internal review to regulatory notification.
After reviewing an alert, a compliance team may decide the activity doesn’t make sense or cannot be reasonably explained. In those cases, the issue is escalated for further investigation, which may include reviewing customer information, transaction history, and any available supporting documentation.
If the investigation confirms potential suspicious activity, the firm will document its findings and file a Suspicious Activity Report (SAR) with FinCEN, as required.
For example, if a customer continues sending small payments to accounts linked to high-risk regions after multiple reviews, that pattern may warrant a SAR. Filing doesn’t mean the firm is accusing the customer of wrongdoing. It means the activity deserves closer attention by authorities.
Clear escalation paths matter here. Teams need to know when to file, who approves reports, and how decisions get documented. Regulators expect consistency and thoughtful judgment, not defensive overreporting.
Recordkeeping and Audit Readiness
Strong recordkeeping supports every part of a CFT program. It allows fintech teams to clearly demonstrate:
What decisions were made
Why those decisions were appropriate
How the team responded when risk emerged
This means maintaining records across the full compliance lifecycle, including customer due diligence, screening results, alerts, reviews, and reports.
For instance, when a team clears a watchlist match, they should document the steps and reasoning behind that decision. Similarly, when activity is escalated, supporting notes should explain what triggered the escalation and how the conclusion was reached.
Beyond day-to-day operations, good records make exams and audits far less disruptive. When regulators ask questions, teams can rely on clear documentation rather than trying to reconstruct decisions after the fact.
Over time, consistent recordkeeping also helps firms identify patterns, strengthen controls, and respond to regulatory scrutiny with greater confidence.
Common Terrorist Financing Methods Financial Institutions Encounter
Terrorist financing doesn’t follow a single pattern. Instead, it shows up through a range of methods that often rely on legitimate channels and everyday financial activity. Below are some of the most common ways financial institutions and fintechs encounter this risk.
1. Use of Cash and Informal Value Transfer Systems
Cash remains one of the simplest tools for terrorist financing. It’s hard to trace and easy to move, especially in regions with limited access to formal banking.
Informal value transfer systems, such as hawala networks, add another layer of risk. These systems move value based on trust and personal relationships rather than formal records. A sender gives cash to a broker in one country, and a recipient collects the equivalent amount from a broker elsewhere.
For financial institutions, these systems can show up indirectly. A fintech may see customers funding accounts with cash through intermediaries or sending payments that align with known informal transfer routes. These patterns don’t always point to wrongdoing, but they often warrant closer review.
2. Abuse of Charities and Nonprofit Organizations
Charities and nonprofit organizations can play an important role in communities, but they can also be misused for terrorist financing. In some cases, bad actors create fake charities. In others, legitimate organizations get exploited without realizing it.
For example, a group might solicit donations for humanitarian aid, then redirect a portion of those funds to support extremist activity. The transactions often look like ordinary charitable giving, which makes them harder to spot through basic screening.
Financial institutions may see this risk when customers send repeated donations to overseas nonprofits in high-risk regions. That activity doesn’t automatically indicate a problem, but it does require context. Understanding the charity’s purpose, location, and history helps teams decide when closer review makes sense.
3. Use of Legitimate Businesses and Front Companies
Terrorist groups sometimes rely on legitimate businesses to move or disguise funds. These businesses may operate openly and generate real revenue, which helps blend illicit activity into normal commercial transactions.
For example, a small trading company might appear to sell goods or services, but part of its revenue gets redirected to support terrorist operations. Payments to suppliers, partners, or overseas affiliates can look routine, even when they serve a hidden purpose.
Fintechs may encounter this risk when business customers move funds in ways that don’t match their stated activities. A company with limited operations sending frequent international payments or routing funds through unrelated entities can raise questions.
Looking at behavior alongside business profiles helps teams spot when something doesn’t add up.
4. Online Fundraising and Social Media Campaigns
Online platforms have made fundraising faster and more accessible. As a result, terrorist groups have exploited websites, messaging apps, and social media to solicit donations from a broad audience.
These campaigns often use emotional messaging tied to current events or humanitarian causes. For example, a post may request small donations to support families in a conflict zone and then direct contributors to payment apps, prepaid cards, or crypto wallets. Individually, each donation appears harmless, but taken together, the volume and coordination can raise concerns.
Fintechs typically encounter this activity through spikes in small incoming or outgoing payments connected to online campaigns. By understanding how funds are promoted and collected online, compliance teams are better equipped to recognize when otherwise normal fundraising behavior begins to present heightened risk.
5. Use of Cryptocurrency and Digital Assets
Cryptocurrency and digital assets can also play a role in terrorist financing. These tools allow value to move quickly across borders, often without the same intermediaries found in traditional finance.
For example, a group may request donations in crypto through online forums or messaging apps. Supporters send small amounts to a wallet address that gets shared widely. Those funds can then be moved through multiple wallets or converted into other assets, which makes tracing harder.
For fintechs and crypto platforms, this risk shows up in wallet activity, transaction patterns, and links to known high-risk addresses. While crypto transactions are recorded on public blockchains, making sense of that data still requires context.
Understanding how digital assets move and how customers use them helps teams decide when activity looks normal and when it deserves closer review.
Key CFT Laws and Regulations
Countering the financing of terrorism is backed by a mix of global standards and local laws. These rules shape how financial institutions and fintechs design controls, monitor activity, and report concerns.
Global Standards and FATF Recommendations
The Financial Action Task Force (FATF) sets the global standards for countering the financing of terrorism. Its recommendations define what effective CFT programs should include and how countries are expected to implement them.
FATF’s guidance covers areas like customer due diligence, sanctions screening, transaction monitoring, and suspicious activity reporting. It also emphasizes understanding risk across products, customers, and geographies, rather than relying on a single set of rules for every firm.
For fintechs, these standards matter because regulators use them as a benchmark. When a country adopts FATF recommendations into local law, fintechs are expected to align their controls with those expectations. That’s why FATF guidance often shows up indirectly during exams, audits, and partner reviews.
United States Laws and Regulatory Framework
In the United States, CFT requirements come from several laws that work together. The most important ones include the Bank Secrecy Act and the USA PATRIOT Act. These laws set the foundation for how financial institutions identify customers, monitor activity, and report suspicious behavior.
Under this framework, fintechs should:
Collect customer information
Screen against sanctions and watchlists
File SARs when needed.
These obligations apply even when funds come from legal sources, and transactions appear routine.
EU and UK Frameworks
The EU and the UK approach CFT through detailed legal frameworks that apply across financial services. These frameworks aim to align with global standards while addressing regional risks and enforcement priorities.
In the EU, counter terrorist financing requirements sit within a series of Anti-Money Laundering Directives. These rules shape how firms conduct customer checks, monitor transactions, and report suspicious activity. The UK follows a similar structure, supported by domestic laws and guidance from UK regulators.
For fintechs operating in these regions, the challenge often comes from variation in how rules get applied. A product that works in one country may trigger different expectations elsewhere. Understanding how local regulators interpret CFT rules helps firms avoid gaps as they expand across markets.
Regulators and Authorities Involved in CFT Enforcement
Countering the financing of terrorism involves more than one regulator or agency. Different authorities play different roles, from collecting reports to supervising firms and investigating criminal activity.
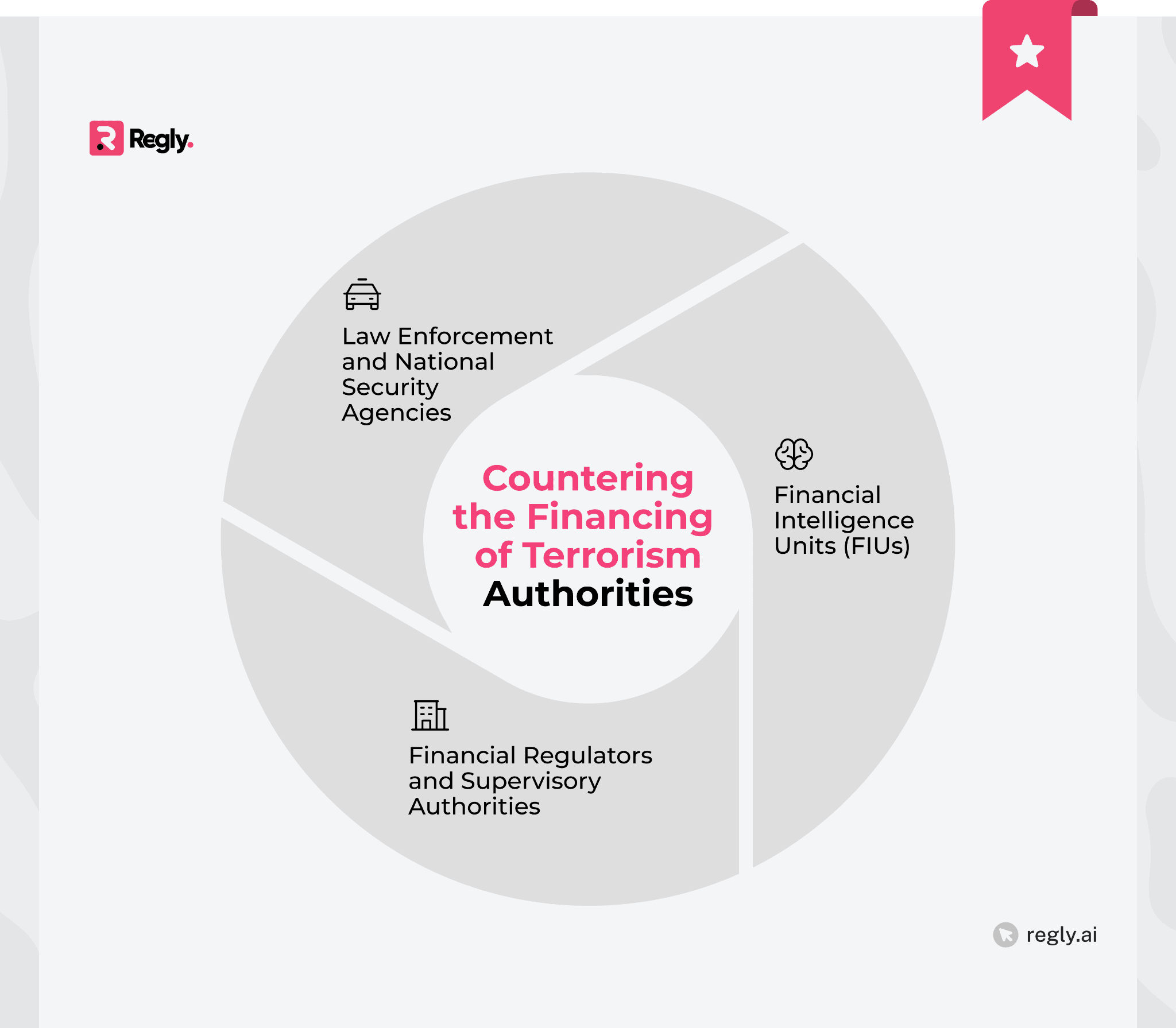
1. Financial Intelligence Units and Suspicious Reporting
Financial Intelligence Units (FIUs) receive and analyze suspicious activity reports from financial institutions. Their role is to:
Identify patterns
Connect information across firms
Share insights with law enforcement when appropriate
In the US, FinCEN acts as the national FIU, while other countries maintain their own counterparts. When a fintech submits a report, it’s not responsible for investigating the activity itself. Instead, the FIU evaluates that information alongside reports from other institutions to understand the broader context.
For example, a single fintech’s report about small overseas transfers may appear limited in isolation. When combined with reports from other firms, however, those details can reveal coordinated activity. This is why timely and accurate reporting is essential to effective CFT efforts at a system-wide level.
2. Financial Regulators and Supervisory Authorities
Financial regulators oversee how firms design and operate their CFT programs. They don’t investigate terrorism directly, but they do examine whether controls work as expected and meet legal requirements.
For fintechs, this often means periodic exams, audits, or licensing reviews. Regulators look at policies, alert handling, and documentation. For example, they may ask how teams review screening matches or decide when to file a suspicious activity report.
Clear processes matter here. When firms can explain how decisions are made and show consistent records, reviews tend to run more smoothly. Regulators focus on how CFT controls operate day to day, not just what’s written in a policy.
3. Law Enforcement and National Security Agencies
Law enforcement and national security agencies investigate terrorist financing once risks move beyond compliance review. They use information from financial intelligence units, regulators, and other sources to build cases and disrupt funding networks.
Fintechs don’t interact with these agencies directly in most situations. Instead, they support investigations through accurate reporting and recordkeeping. For example, when a firm files a SAR, that information can later support an investigation across multiple institutions.
Understanding this role helps fintech teams see why timely reporting and clear documentation matter. Even routine compliance actions can contribute to broader efforts to stop terrorist financing.
Countering the Financing of Terrorism in Fintech and Crypto
Fintech and crypto products introduce new ways to move value, which also changes how terrorist financing risk shows up. These products can increase speed, reach, and complexity, making tailored CFT controls especially important.
Fintech-Specific CFT Risk Factors
Fintech products often change how quickly and easily money moves. That can introduce CFT risks that don’t always exist in traditional financial services.
Fast onboarding is one example. When customers can open accounts in minutes, teams have less time to understand who’s behind the activity. If identity checks or risk assessments are too light, bad actors can slip through early and stay active longer than expected.
Product design also matters. Features like instant transfers, peer-to-peer payments, or global access can make it easier to move funds across borders with little friction. A user sending repeated small payments to multiple countries through a single app may raise very different concerns than the same behavior in a slower, more restricted system.
Fintechs also tend to serve a wide mix of customers. Individuals, startups, nonprofits, and global businesses may all use the same platform. That diversity makes it harder to define what “normal” activity looks like, which is why CFT controls need to reflect how each product and customer type actually operates.
Terrorist Financing Risks in Cryptocurrency
Cryptocurrency creates a different risk profile than traditional finance. Transactions move quickly, cross borders easily, and don’t rely on the same intermediaries that banks do.
Terrorist groups may use crypto to collect donations or move funds without using the banking system. For example, a group might post a wallet address online and ask supporters to send small amounts. Those funds can then move through multiple wallets or be converted into other assets.
For fintechs and crypto platforms, the challenge isn’t visibility. Blockchains are public. The challenge is interpretation.
A wallet receiving frequent small transfers from unrelated sources may look unusual, but context matters. Understanding customer behavior, wallet history, and connections to known risk indicators helps teams decide when activity deserves closer review.
Travel Rule and Blockchain Monitoring Requirements
The Travel Rule adds another layer to CFT obligations for fintechs and crypto platforms. It requires firms to share certain customer information when funds move between institutions, especially for virtual asset transfers.
In practice, this means collecting and transmitting details about the sender and recipient when transactions meet specific thresholds. For example, a crypto transfer between two platforms may require both sides to exchange identifying information, even though the transaction itself happens on a public blockchain.
Blockchain monitoring complements this requirement. Tools track wallet activity, identify links to high-risk addresses, and flag patterns tied to known threats. Together, these controls help fintechs understand who’s involved in a transaction and how funds move over time, which supports more informed CFT reviews.
Common CFT Compliance Challenges for Fintech Companies
Building and maintaining a CFT program isn’t always straightforward for fintechs. Rapid growth, new products, and evolving regulations can make even well-designed controls hard to manage.
Identifying Terrorist Financing Without Obvious Red Flags: Terrorist financing often involves lawful funds and everyday transactions. Small payments, routine transfers, or charitable donations may not look risky on their own, which makes it harder for teams to know when to take a closer look.
Managing Alerts, False Positives, and Manual Reviews: Screening and monitoring systems can generate a high volume of alerts. Many turn out to be false positives, but each one still needs review. This can strain small compliance teams and slow response times as transaction volume grows.
Navigating Cross-Border and Jurisdictional Differences: Fintechs that operate across countries face different CFT rules, thresholds, and reporting requirements. A process that works in one jurisdiction may not meet expectations in another, which creates complexity as firms expand.
Scaling CFT Controls With Business Growth: Early-stage controls often don’t hold up as products, customers, and transaction volumes increase. What worked for a single product or market can break down once a fintech adds new features, regions, or customer types.
Limited context around customer behavior: Fintechs don’t always have the same depth of customer information as traditional banks. When activity looks unusual, teams may struggle to understand intent without clear behavioral baselines.
Balancing user experience with compliance controls: Fast onboarding and low-friction payments are core to many fintech products. Adding stronger CFT controls can create tension between compliance needs and customer expectations if not designed carefully.
Keeping controls aligned with product changes: Fintech products evolve quickly. New features, new payment flows, or new asset types can introduce risk before controls are updated, especially when compliance isn’t involved early in product design.
Resource constraints within compliance teams: Many fintechs operate with small compliance teams. Reviewing alerts, documenting decisions, and staying current on regulatory changes can stretch resources thin without the right processes in place.
How Can Fintechs Build a Practical CFT Program?
A workable CFT program starts with understanding how your product actually moves money. Controls should reflect real user behavior, real transaction flows, and real risks, not generic checklists copied from traditional banks.
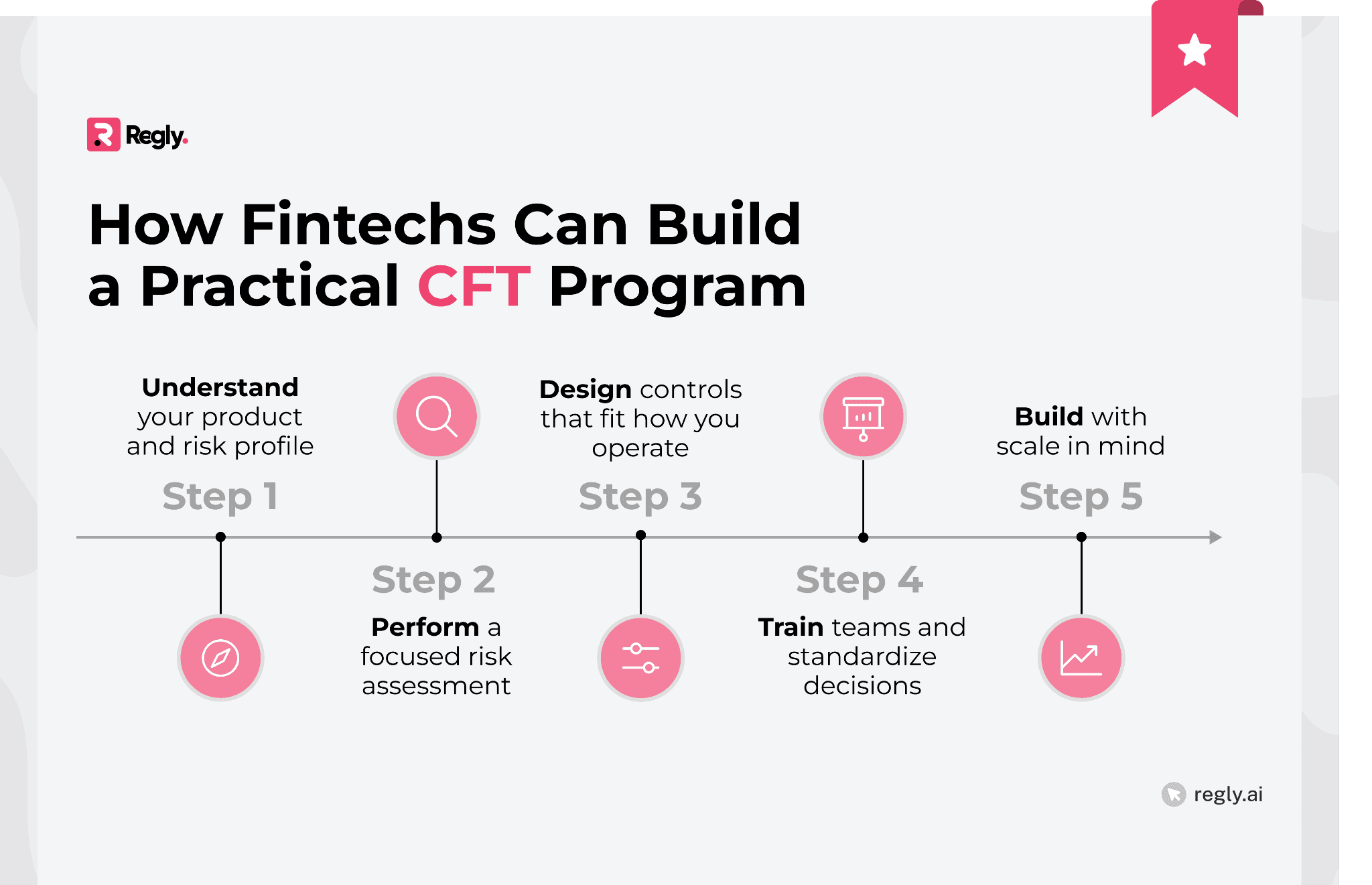
Step 1: Understand Your Product and Risk Profile
Start by mapping how funds move through your product from start to finish. Look at who your customers are, how they onboard, where money enters and exits, and which features reduce friction. A domestic payments app faces very different CFT risk than a crypto platform with global users, even if both handle similar transaction volumes.
Step 2: Perform a Focused Risk Assessment
Assess risk across customers, products, geographies, and delivery channels. Focus on where terrorist financing could realistically occur based on how your platform is used, not just where regulations say risk might exist. This assessment should guide how much scrutiny different activities receive and where controls need to be stronger.
Step 3: Design Controls That Fit How You Operate
Build customer due diligence, screening, and monitoring processes that align with actual transaction behavior. Clear escalation paths, defined ownership, and consistent documentation help teams respond quickly when issues arise, without adding unnecessary complexity to everyday operations.
Step 4: Train Teams and Standardize Decisions
Make sure compliance and operations teams understand what terrorist financing risk looks like in the context of your product. Ongoing training and shared review standards reduce guesswork, improve alert quality, and support more consistent decisions across the team.
Step 5: Build With Scale in Mind
As transaction volume and product complexity grow, manual processes become harder to manage. Many fintechs adopt tools that automate repeat tasks, centralize documentation, and support consistent workflows. Platforms like Regly focus on practical, process-driven controls that help teams scale without adding large in-house compliance teams.
FAQs About Countering the Financing of Terrorism (CFT)
1. What are the 4 P’s of counter-terrorism?
The four P’s of counter-terrorism are Prevent, Pursue, Protect, and Prepare. Together, they describe how governments work to reduce terrorism risk, disrupt activity, protect systems, and respond when incidents occur. In financial services, CFT efforts mainly support the Pursue pillar by helping track and disrupt terrorist funding.
2. What are the main points of the Counter Terrorism and Security Act 2015?
The Counter Terrorism and Security Act 2015 strengthens the UK’s approach to preventing terrorism. It expands monitoring, reporting, and cooperation requirements for organizations, including financial institutions, to help identify and reduce terrorism related risk.
3. What is the purpose of CFT regulations?
CFT regulations aim to stop terrorist groups from raising or moving funds through the financial system. They focus on identifying risk, reporting suspicious activity, and disrupting funding networks rather than proving intent or criminal guilt.
Ready to Get Started?
Schedule a demo today and find out how Regly can help your business.