A vendor compliance checklist matters because most fintechs never operate in isolation.
From cloud providers and payment processors to analytics tools and customer support platforms, third-party vendors are woven into everyday operations. And when something goes wrong, regulators almost always start by asking how those vendors were chosen, monitored, and documented.
For founders, legal teams, and compliance officers, vendor oversight can feel frustratingly unclear. Everyone knows it matters, but guidance is often vague and easy to overthink. Add limited time, lean teams, and tight budgets, and it quickly becomes overwhelming.
In this guide, we’ll break down vendor compliance into a practical, manageable approach that works in real-world fintech environments.
What Vendor Compliance Means (and Why Regulators Care)
Vendor compliance is about how a regulated firm manages the risks that come with relying on third parties. That includes:
How vendors are chosen
What they are permitted to do
How they handle sensitive data
How their performance is monitored over time.
Simply put, regulators want to see that you understand who supports your business and how those relationships affect your regulatory responsibilities.
Regulators make one thing clear: outsourcing a function does not outsource responsibility. If a vendor handles customer data, touches funds, supports onboarding, or influences disclosures, accountability still sits with the regulated firm, regardless of how established or widely used that vendor may be.
Regulators pay close attention to vendor compliance because third parties are often where issues begin. When firms don’t properly monitor their vendors, problems tend to show up as data breaches, misleading marketing, weak AML controls, or service outages.
In exams, regulators usually trace these outcomes back to gaps in vendor due diligence, contract terms, or ongoing monitoring, and view them as signs that internal controls need strengthening.
Regly’s vendor management tool supports compliance by organizing vendor inventories, risk assessments, contracts, and compliance documentation into a single system, making it easier to demonstrate consistent oversight during audits and exams.
Core Regulations That Shape a Vendor Compliance Checklist
Vendor compliance is not tied to one specific rule or regulator. Instead, expectations come from different areas of regulation, including financial services, consumer protection, and data privacy.
US Regulatory Expectations
In the US, vendor compliance expectations span multiple regulatory frameworks. While the language varies by regulator, the underlying expectations are essentially the same. Below are the key areas regulators tend to focus on.
Risk-based vendor due diligence: Before bringing a vendor on, firms need to evaluate the risk that the vendor introduces. Vendors involved in regulated activities, customer data, or funds movement warrant a closer look than those providing back-office tools with limited access.
Clear documentation and records: Regulators want to see written risk assessments, contracts, and supporting materials that explain why a vendor was approved and how risks are being managed. Checking a box that says "review completed" is not enough.
Ongoing oversight and monitoring: Vendor review does not end once onboarding wraps up. Firms should track performance, stay aware of service changes, and revisit risk assessments periodically, especially when a vendor takes on a larger role.
Appropriate contractual controls: Contracts should include provisions related to compliance obligations, data protection, audit rights, and termination. Regulators often review agreements to confirm these controls are in place.
Accountability for vendor actions: Even when a vendor performs a function on the firm’s behalf, the regulated entity remains responsible. Regulators focus on whether the firm can explain and defend vendor-related decisions during an exam.
For fintechs, these expectations often extend into technology, cybersecurity, and customer communications.
Global Regulatory Expectations
Vendor compliance expectations extend well beyond US regulators. Fintechs that operate internationally, rely on offshore vendors, or handle data connected to non-US customers are often subject to global standards as well.
Shared Principles Across Global Frameworks
Most international regulatory regimes reinforce a few common expectations around vendor oversight.
Responsibility remains with the regulated firm: Outsourcing a function doesn’t mean outsourcing accountability. Even when services are delivered from another country, regulators still hold the firm responsible for what vendors do.
Risk-based oversight: Vendors that support regulated activities, interact with customers, or keep critical operations running need deeper review and more frequent check-ins. Vendors with a smaller footprint can usually get by with lighter controls.
Data protection and access controls: Regulators expect you to know where data is stored, who can access it, and how it’s protected. Cross-border data transfers and remote access are frequent areas of focus.
Ongoing monitoring and change management: Vendor risk is not static. Material changes to services, ownership, subcontractors, or geographic footprint are expected to trigger reassessment and updated documentation.
Key Risks to Cover in Vendor Compliance
Not all vendors create the same level of risk. A strong vendor compliance checklist helps teams focus on the risks that matter most to regulators, customers, and the business, without overcomplicating oversight.
Here are the key risk areas most fintechs should evaluate when managing vendor relationships.
Risk Area | What Regulators Focus On |
|---|---|
Operational Risk | Reliability, uptime, escalation |
Cybersecurity & Data | Data access, storage, breach response |
Financial Crime & AML | KYC, monitoring, alerts |
Consumer Protection | Marketing claims, customer treatment |
Business Continuity | Outages, backups |
Fourth-Party Risk | Subcontractors, dependencies |
Operational Risk
Operational risk looks at whether a vendor can reliably do what you depend on them to do. If a service fails, slows down, or becomes unavailable, the impact often shows up in customer experience or internal workflows.
For example, a payments processor or core banking provider supports daily, customer-facing activity. If that vendor has an outage, customers may not be able to move funds or complete transactions. That makes operational reliability a regulatory and business concern.
When reviewing operational risk, teams typically look at:
What function the vendor supports, and how critical it is
Service uptime commitments and incident response expectations
How issues are escalated and communicated
Whether there is a backup or alternative if the vendor fails
A vendor compliance checklist should reflect how essential their service is. Clearer documentation and more frequent reviews should be required for vendors supporting core operations than those providing non-essential services.
Cybersecurity and Data Protection
Vendors that have access to customer data, internal systems, or sensitive business information can introduce cybersecurity and data protection risks. Regulators pay close attention to this area because many major compliance failures start with weak vendor controls.
For example, a cloud hosting provider, CRM platform, or identity verification vendor may store or process customer data. If that data is mishandled or exposed, the regulated firm is still accountable, even if the incident happened on the vendor’s systems.
When reviewing this risk, teams usually focus on:
What data the vendor can access, and how sensitive it is
Where data is stored and whether it crosses borders
How access is controlled, monitored, and revoked
Whether the vendor has experienced past security incidents
A practical checklist doesn’t require deep technical testing for every vendor. Instead, it helps teams confirm that higher-risk vendors follow reasonable security practices and that those expectations are documented and revisited over time.
Financial Crime and AML
Financial crime and AML risk come into play when a vendor touches customer onboarding, transactions, monitoring, or investigations. If a vendor plays a role in identifying or managing financial crime risk, regulators will want to see that you are actively overseeing that relationship.
For example, many fintechs rely on third parties for identity verification, transaction monitoring, sanctions screening, or fraud detection. When those tools miss red flags or apply weak controls, the regulated firm still owns the outcome.
When reviewing this risk, teams typically consider:
Whether the vendor supports AML, KYC, or fraud-related functions
How the vendor’s controls align with the firm’s own risk profile
The data and decision-making that the vendor influences
How issues, alerts, or failures are reported and reviewed
A vendor compliance checklist helps document how these vendors were evaluated and why their controls were considered appropriate. This documentation is often critical during exams, especially when regulators ask how third-party tools fit into the firm’s overall AML program.
Consumer Protection and Marketing Practices
Consumer protection risk arises when vendors influence how products are presented to customers or how customers are treated. Regulators care about this because misleading statements or unfair practices sometimes start outside the regulated firm.
For example, a marketing agency may draft website copy, email campaigns, or paid ads. A customer support vendor may handle complaints or respond to disputes. If messaging is inaccurate or customer issues are mishandled, the regulated firm is still accountable.
When reviewing this risk, teams usually look at:
Whether the vendor creates or approves customer-facing content
How disclosures, claims, and promotions are reviewed
How customer complaints or disputes are handled
Whether there is oversight of scripts, templates, or workflows
A good vendor compliance checklist helps teams track which vendors touch customers and what guardrails are in place. This makes it easier to explain how marketing and customer interactions are monitored during a regulatory exam.
Business Continuity and Concentration Risk
Business continuity risk focuses on what happens if a vendor can’t operate as expected. Concentration risk, on the other hand, examines the extent to which your business relies on a single provider.
For example, if one cloud provider supports most of your core systems, an outage or service disruption could affect onboarding, transactions, and customer support all at once. Even a short disruption can create regulatory and reputational issues.
When reviewing this risk, teams often consider:
How critical the vendor is to daily operations
Whether backup providers or internal workarounds exist
How quickly can services be restored after an incident
How much of the business relies on one vendor or one region
A vendor compliance checklist helps teams keep track of these dependencies and think through what could realistically go wrong. That preparation often matters more to regulators than having a perfect contingency plan on paper.
Fourth-Party and Supply Chain Risk
Fourth-party risk comes from the vendors your vendors rely on. Even if you don’t contract with them directly, their failures can still affect your business.
For example, a KYC provider might rely on external data sources or subcontract parts of its screening process. If one of those providers has an outage or data issue, your onboarding process could be disrupted without much warning.
When reviewing this risk, teams usually look at:
Whether vendors rely on subcontractors to deliver services
How much visibility the firm has into those relationships
Whether vendors are required to notify you of material changes
How issues tied to subcontractors are escalated and resolved
An effective vendor compliance checklist shouldn’t map every single dependency. It should help teams identify where fourth-party risk is meaningful and confirm that higher-risk vendors are managing their own supply chains responsibly.
—
Regly’s vendor management tool helps teams track these risk areas within each vendor profile, so changes to services, data access, or dependencies can be reviewed and documented in one place over time.
The Vendor Compliance Checklist (By Vendor Tier)
Breaking your vendor compliance checklist into tiers helps you focus oversight where it matters most, without spending unnecessary time on low-risk relationships. Below is a practical way to structure vendor reviews based on how critical each vendor is to your business.
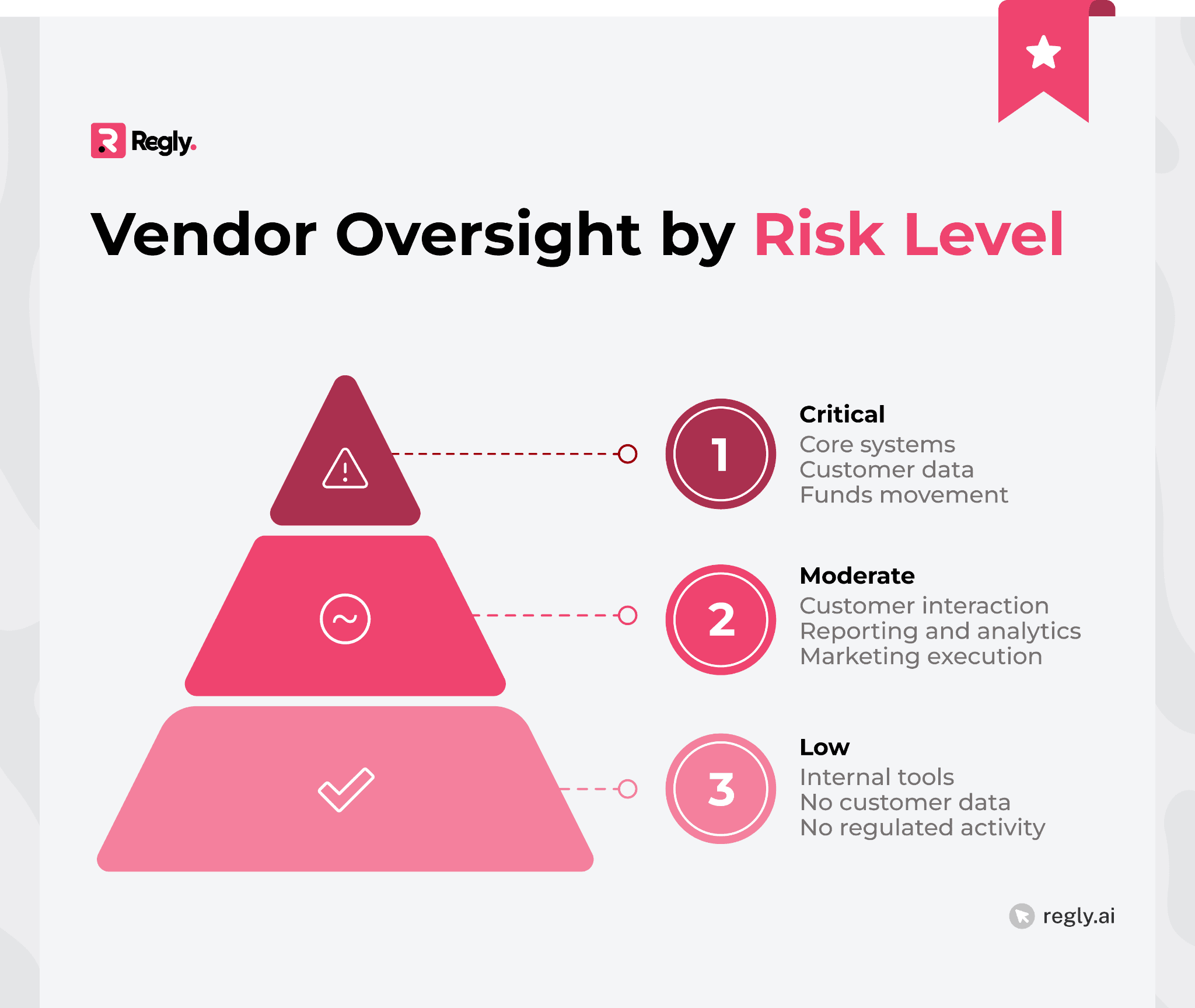
Tier 1: Critical Vendors
Tier 1 vendors support functions that are essential to your operations or regulatory obligations. If one of these vendors fails, customers are likely affected, and regulatory questions usually follow.
Common examples include core banking platforms, payment processors, cloud infrastructure providers, KYC or AML systems, and customer data platforms.
A vendor compliance checklist for Tier 1 vendors typically covers:
A detailed risk assessment tied to the vendor’s role
Review of security, data protection, and compliance controls
Clear contractual terms around responsibilities and audit rights
Ongoing monitoring, not just a one-time review
Documented incident response and escalation processes
For example, your cloud provider hosts customer data. You’ll need to explain to regulators how you control access, handle outages, and review risks over time. Tier 1 oversight should be thorough, documented, and revisited regularly.
Tier 2: Moderate-Risk Vendors
Tier 2 vendors support important functions, but they don’t usually touch core systems or directly control regulated activity. Issues with these vendors can still create problems, but the impact is often more limited.
Examples might include CRM tools, analytics platforms, customer support services, or marketing vendors that help execute campaigns but don’t set strategy.
A vendor compliance checklist for Tier 2 vendors often includes:
A documented risk review that matches the vendor’s role
Confirmation of basic security and data handling practices
Contract terms that define responsibilities and limits
Periodic check-ins to confirm the service hasn’t changed
For example, a customer support vendor may not handle funds, but they do interact with customers. Oversight should focus on training, scripts, and escalation procedures, without applying the same depth of review used for core systems.
Regly’s vendor management solution supports this tiered approach by allowing teams to assign risk levels, document services provided, and link contracts and supporting materials directly to each vendor.
Tier 3: Low-Risk Vendors
Tier 3 vendors support routine business activities and don’t meaningfully affect regulated operations. These relationships still belong in your vendor inventory, but they usually don’t require ongoing compliance review.
Common examples include scheduling tools, internal collaboration software, design firms, or HR vendors that don’t access customer data.
A vendor compliance checklist for Tier 3 vendors often includes:
Basic details about the vendor and the service provided
Confirmation that no customer data or regulated activity is involved
A simple review of standard terms or contracts
For example, a design vendor creating brand assets with no access to systems or customer information presents limited risk. Documenting the scope of the relationship is typically enough unless that scope changes.
Common Pitfalls and Misconceptions in Vendor Oversight
Most vendor compliance issues don’t come from ignoring oversight altogether. They come from well-intentioned processes that don’t match how fintechs actually operate. Regulators tend to flag the same patterns again and again.
Below are the most common vendor oversight pitfalls, grouped by where things usually break down.
1. Weak or Undefined Vendor Scoping
Many firms struggle to clearly describe their vendors’ roles. When descriptions are vague, outdated, or borrowed from marketing language, it becomes difficult to assess risk or explain those relationships to regulators during an exam.
Why it matters: If you can’t clearly define a vendor’s role, regulators will assume risk hasn’t been fully considered.
Example: A fintech lists a vendor as providing “analytics support,” but the vendor also has access to raw customer data. That gap between description and reality immediately raises questions about data protection, access controls, and oversight.
2. Risk Tiering That Exists Only on Paper
Some firms create vendor tiers but struggle to use them in practice. Vendors either receive the same level of review across the board, or tiers are set once and never updated. Eventually, the tiering stops matching reality.
Why it matters: Risk-based oversight is a core regulatory expectation. Inconsistent tiering suggests the framework isn’t actually driving decisions.
Example: A customer support vendor initially handles basic inquiries and is classified as low risk. Over time, the vendor begins managing customer complaints and disputes, gaining access to sensitive data and influencing regulatory communications. Because the tiering is never revisited, the vendor remains classified as low risk, leaving increased risk unaddressed.
3. Over-Reliance on Vendor Reputation
It is common to assume that well-known vendors are low risk. However, a strong brand, solid funding, or widespread industry use does not eliminate the need to understand how that vendor supports your business.
Why it matters: Regulators care about your controls, not the vendor’s market position.
Example: A firm approves a large cloud provider mainly based on name recognition, without clearly documenting data access, where data is stored, or incident response expectations. During an exam, the firm is unable to clearly explain those details, raising concerns about oversight and data protection.
4. One-Time Due Diligence With No Ongoing Review
Many vendor programs are built around onboarding but lack ongoing follow-up. Over time, as services expand, ownership changes, or data access increases, the initial review no longer reflects reality.
Why it matters: Vendor risk changes over time. Regulators expect firms to notice and respond to those changes.
Example: A firm approves a fraud vendor to provide basic transaction monitoring and classifies it as medium risk. Over time, the vendor adds new tools that influence customer approvals and declines, directly affecting customer outcomes. Because the firm never reassesses the vendor’s role or updates its documentation, it can’t explain how those expanded services are overseen when questioned by regulators.
5. Contract Reviews That Miss Compliance Reality
Contracts are reviewed, but compliance isn’t always part of the conversation. As a result, agreements may be signed without checking whether audit rights, data obligations, or termination terms meet regulatory expectations.
Why it matters: During exams, regulators often review contracts to confirm oversight isn’t just conceptual.
Example: A vendor handles sensitive customer data, but the contract doesn’t clearly define breach-notification timelines, data-access limitations, or audit rights. When asked during an exam, the firm can’t point to contractual protections that support its oversight framework.
6. Poor Documentation of Decisions
Teams regularly make sound, risk-based decisions, but the rationale isn’t always documented. When staff turnover occurs or exams happen, it becomes hard to explain how and why those decisions were made.
Why it matters: If you can’t show how a decision was made, regulators treat it as if it wasn’t made at all.
Example: A firm classifies a vendor as moderate risk but doesn’t document why enhanced due diligence wasn’t required. During an exam, the firm struggles to explain the rationale, raising questions about whether the risk assessment was fully considered.
7. Ignoring Fourth-Party Dependencies
Subcontractors rarely come up in vendor discussions unless there is a problem. As a result, firms may not fully understand whether their critical vendors rely on third parties or how those relationships are overseen.
Why it matters: Fourth-party failures can affect your business just as directly as primary vendor failures.
Example: An identity verification provider relies on external data sources to complete customer checks. When one of those data sources experiences an outage, onboarding is disrupted without warning, and the firm is left unable to explain how those dependencies are monitored or managed.
—
A vendor compliance checklist works best when it reflects how your business actually operates. Regulators aren’t looking for perfect paperwork or exhaustive files on every vendor. They want to see that risks are understood, decisions are made deliberately, and oversight increases as a vendor’s impact grows.
For most fintechs, the real challenge is not knowing what regulators expect, but keeping vendor oversight consistent as the company scales, vendors evolve, and teams remain lean. This is where structured tooling can make a real difference.
Platforms like Regly bring vendor inventories, risk assessments, and documentation into one place, making vendor oversight easier to manage and explain. That kind of clarity supports a compliance program that’s scalable and potentially aligned with regulatory expectations.
Ready to Get Started?
Schedule a demo today and find out how Regly can help your business.